- Security+ SY0-601 Certification
- Security+ SY0-601: Passing the Security+ Exam
- Security+ SY0-601: Definitions and Catchwords
- Security+ SY0-601: 1.0 Threats, Attacks, and Vulnerabilities
- Security+ SY0-601: 1.1 Social Engineering Techniques
- Security+ SY0-601: 1.2 Indicators of Attack
- Security+ SY0-601: 1.3 Application Attacks
- Security+ SY0-601: 1.4: Network Attack Indicators
- Security+ SY0-601: 1.5: Threat Actors, Vectors, and Intelligence Sources
- Security+ SY0-601: 1.6: Vulnerabilities
- Security+ SY0-601: 1.7: Security Assessment
- Security+ SY0-601: 1.8: Penetration Testing
- Security+ SY0-601: 2.0 Architecture and Design
- Security+ SY0-601: 2.1 Enterprise Security Architecture
- Security+ SY0-601: 2.2: Virtualization and Cloud Security
- Security+ SY0-601: 2.3: Secure Application Development, Deployment and Automation
- Security+ SY0-601: 2.4: Authentication and Authorization
- Security+ SY0-601: 2.5: Implementing Cybersecurity Resilience
- Security+ SY0-601: 2.6: Embedded and Specialized Systems
- Security+ SY0-601: 2.7: Physical Security Controls
- Security+ SY0-601: 2.8: Cryptography
- Security+ SY0-601: 3.0: Implementation
- Security+ SY0-601: 3.1 Secure Protocols
- Security+ SY0-601: 3.2: Host and Application Security
- Security+ SY0-601: 3.3: Secure Network Design
- Security+ SY0-601: 3.4: Wi-Fi Security
- Security+ SY0-601: 3.5: Secure Mobile Solutions
- Security+ SY0-601: 3.6: Cybersecurity Solutions in the Cloud
- Security+ SY0-601: 3.7: Identity and Account Management Controls
- Security+ SY0-601: 3.8: Implement Authentication and Authorization Solutions
- Security+ SY0-601: 3.9: Public Key Infrastructure
- Security+ SY0-601: 4.0: Operations and Incident Response
- Security+ SY0-601: 4.1: Tools to Assess Organizational Security
- Security+ SY0-601: 4.2: Policies, Processes, and Procedures for Incident Response
- Security+ SY0-601: 4.3: Appropriate Data Sources for Investigation
- Security+ SY0-601: 4.4: Mitigation Techniques
- Security+ SY0-601: 4.5: Digital Forensics
- Security+ SY0-601: 5.0: Governance, Risk, and Compliance
- Security+ SY0-601: 5.1: Types of Controls
- Security+ SY0-601: 5.2 Regulations, Standards, and Frameworks
- Security+ SY0-601: 5.3: Policies and Organizational Security
- Security+ SY0-601: 5.4: Risk Management Processes and Concepts
- Security+ SY0-601: 5.5: Privacy and Sensitive Data
- Security+: My Favorite Free Tools
- Security+ : Sample Questions
- Passing the CompTIA Exams
- Understanding CompTIA Objectives Using Bloom’s Taxonomy
Chapter 15: Physical Security Controls
Bollards/barricades
Access control vestibules (Remember: these are no longer called “man-traps” in CompTIA nomenclature.)
Badges
Alarms
Signage
Cameras
Motion recognition
Object detection
Closed-circuit television (CCTV)
Industrial camouflage
Personnel
Guards
Robot sentries
Reception
Two-person integrity/control
Locks
Biometrics
Electronic
Physical
Cable locks
Kensington slots
USB data blocker
https://www.amazon.com/Blocker-JSAUX-Charge-Only-Blocking-Compatible/dp/B0897WB3VJ
Lighting
Fencing
Fire suppression
Chemical agents
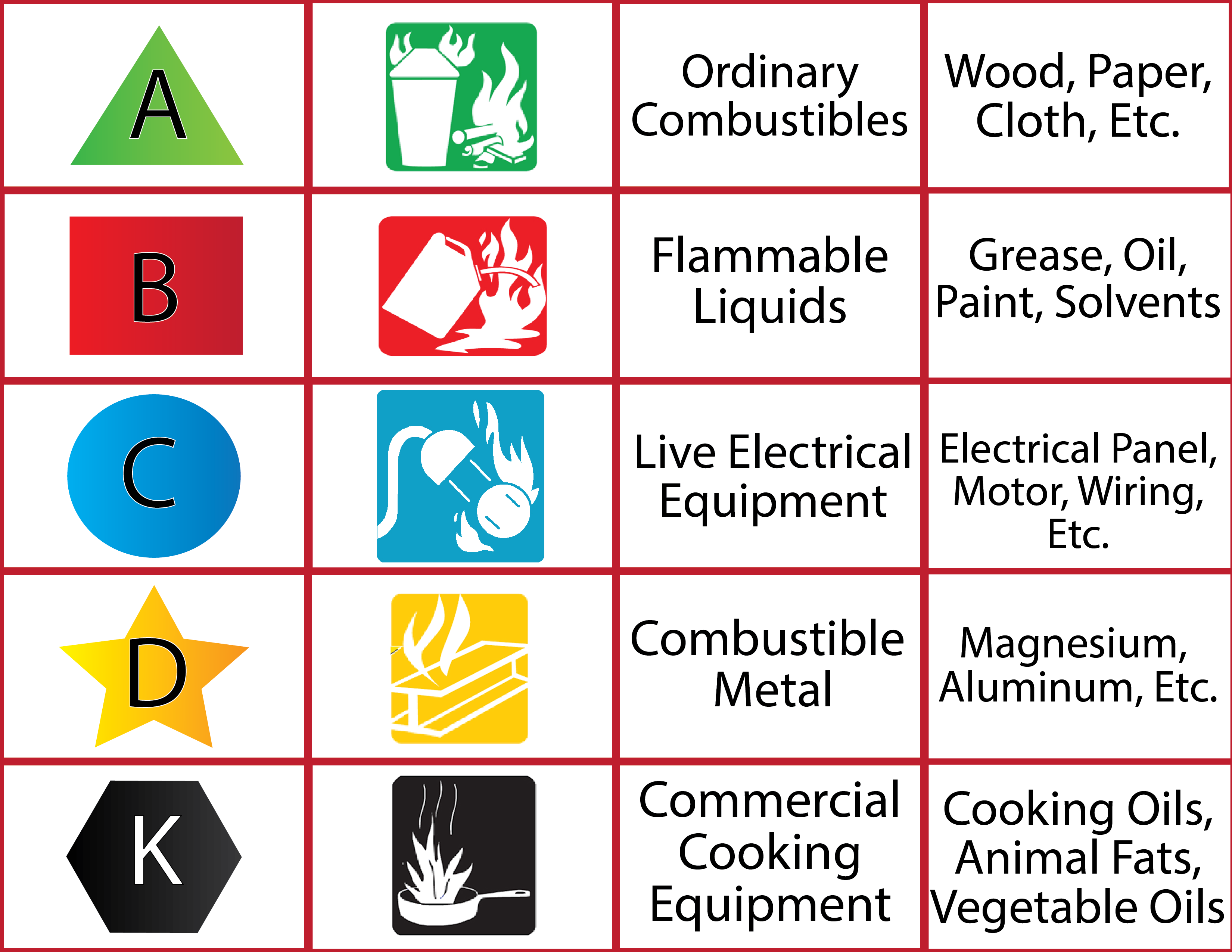
Fire extinguisher types: A B C D K
Sensors
Motion detection
Noise detection
Proximity reader
Moisture detection
Cards
Temperature
Drones
Surveillance!
Visitor logs
Faraday cages
Air gap
Screened subnet (previously known as demilitarized zone)
What CompTIA means here is “Controlled Access Areas”
Protected cable distribution
https://en.wikipedia.org/wiki/Protective_distribution_system
Secure areas
Air gap
Vault
Safe
Hot aisle
Cold aisle
Secure data destruction
Burning
Shredding
Pulping
Pulverizing
Degaussing
Third-party solutions
Vocabulary
FRR: False Rejection Rate
FAR: False Acceptance Rate
CER: Crossover Error Rate
Security Controls By Type
Physical Measures
locks
Technical Measures
smart cards, biometrics
Operational Measures
policies and procedures
Interesting Inside Information Attacks
Cyber lock locksmith codes
Elevator codes, eg. Door Close + Floor
